[SOLVED] PiVPN with PiHole home server. UT client configuration [step-by-step]
-
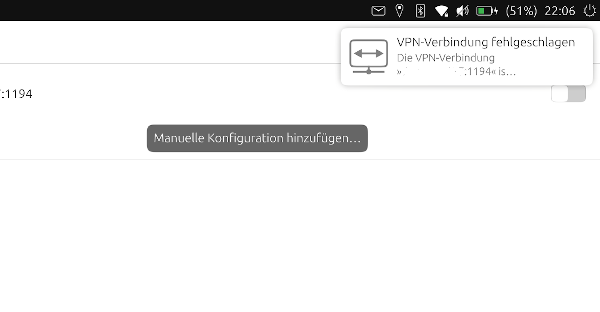
I tested again, with the same result. I get an error message, that is displayed only partly, although on my tablet screen there is enough space to display a complete article ...
-
@BigB I don't know I could help you or not but I want to know this
.
Can Desktop Linux with the generated .pem files connect successfully to PiVPN server from outside of LAN? -
@BigB Hi,
I'm running pivpn+pihole (Ubuntu server on my Pi) on my UT phone (N5) successfully ( step by step below )- Install pihole first, this will allow you to use the install procedure without having to edit config files:
pivpn documentation: https://github.com/pivpn/pivpn/wiki/OpenVPN
curl -sSL https://install.pi-hole.net | bash- Install pivpn: make sure you've selected local dns (pihole) and disable elliptic curve cryptography (ECC), because ECC is not supported on the old version of OpenVPN on UT. Also make sure you've selected OpenVPN, not Wireguard.
curl -L https://install.pivpn.io | bash- Open port 1194 (default) on your router. A domain with DDNS is also useful if you don't have a static IP, else you have to change the IP in the settings each time your connection changes IP.
- Add the client to pivpn ( don't use special characters in the password or username, just letters and numbers)
more info on alphanumeric pw and user: https://forums.ubports.com/topic/2188/solved-vpn-no-vpn-secrets-error
pivpn add- Get the ovpn file from your pi and extract files:
ca.crt <- all the content between <ca> and </ca> client.crt <- all the content between <cert> and </cert> client.key <- all the content between <key> and </key> ta.key <- all the content between <tls-auth> and </tls-auth>- copy the 4 files in ~/.cert/nm-openvpn on your phone
- create a new vpn connection in the settings using the following settings:
Server: your public ip
Port: 1194 (default)
Type: OpenVPN
Protocol: UDP
Auth type: Certificates (TLS)
Client certificate: client.crt
Private key: client.key
Password: (password of the client)
CA certificate: ca.crt
Use additional TLS authentication: yes
TLS key: ta.key
Key direction: 1
Verify peer certificate: yes
Peer certificate TLS type: Server
Cipher: AES-256-CBC
Compress data: no (doesn't seem to work)
If it still doesn't work, please post the content of the following command when you are trying to connect to the VPN:
tail -f /var/log/syslog - Install pihole first, this will allow you to use the install procedure without having to edit config files:
-
In my case syslog shows:
NetworkManager ... result="success"
... Started the VPN service ...
... Saw the service appear; activating connection ...
... <error> ... vpn-connection ... Failed to request VPN secrets #3: No agents were available for this request. -
@herr-b Can you check if running the following command works:
sudo openvpn myfile.ovpn -
@Capsia yes this command works, I can enter the password and at the end it confirms "Initialization Sequence Completed". On the pivpn I see the connected device. But opening Morph Browser the traffic is not routed via the pihole. So I suppose, that I make something wrong with the "Manual Configuration" or the four files.
It is a little bit confusing, that the configuration never remembers the settings: "key-direction 1" and "cipher AES-256-CBC" when I edit the connection.
-
@herr-b It's ok that the traffic isn't routed to the vpn, the command is just creating the connection between UT and the VPN server to check if the settings are supported in the previous version of OpenVPN (installed on UT).
To check if the configuration is ok and it is saved in the settings follow the procedure:
- Find the id (UUID) of your vpn connection running:
nmcli c- Run the following command and check your config:
nmcli --show-secrets c show CONNECTION_IDCheck the vpn.data and vpn.secrets fields:
vpn.data: ta = /home/phablet/.cert/nm-openvpn/ta.key, cert = /home/phablet/.cert/nm-openvpn/client.crt, dev = tun, key = /home/phablet/.cert/nm-openvpn/client.key, ca = /home/phablet/.cert/nm-openvpn/ca.crt, remote-cert-tls = server, cert-pass-flags = 0, cipher = AES-256-CBC, remote = YOUR_IP_OR_DOMAIN:1194, auth = SHA256, connection-type = tls, ta-dir = 1 vpn.secrets: cert-pass = YOUR_SECRET_PASSWORDIf the fields are wrong you can force the config running:
nmcli c modify CONNECTION_ID vpn.data "auth = SHA256, ca = /home/phablet/.cert/nm-openvpn/ca.crt, cert = /home/phablet/.cert/nm-openvpn/client.crt, cert-pass-flags = 0, cipher = AES-256-CBC, connection-type = tls, dev = tun, key = /home/phablet/.cert/nm-openvpn/client.key, remote = YOUR_IP_OR_DOMAIN:1194, remote-cert-tls = server, ta = /home/phablet/.cert/nm-openvpn/ta.key, ta-dir = 1"In case no secret is saved
nmcli c modify CONNECTION_ID vpn.secrets "cert-pass = YOUR_SECRET_PASSWORD" -
@Capsia
I really Thank You!
I believe it'll be solution, because I have enabled ECC during installation.
Unfortunately I can reinstall and check if it works soonest on Sunday.Some questions before reinstalling:
- When I disable EEC, does traffic'll be still encrypted somehow?
- Can I pick and forward my custom port for VPN, just not to leave it default?
- If it works for me, could you allow me to copy your solution to 1st post, to be easy accessible for others? Of course I'll mark that You found the solution.
Once again, big big thanks!
-
- Yes traffic is still encrypted, ECC is used to make smaller certificates and faster cryptography for clients that support it. UT doesn't support it yet, in the future the openvpn package might get an update so that we can benefit of the latest improvements.
- I haven't tried changing port, but it should work. Also change the configs accordingly.
- Yes

-
@Capsia yes for me it seems to work now! I checked the config according to your advice and the fields where different, secrets was empty. I also added the port according to @thilov and entered directly myurl.com:1194
Then I forced the config and secret with your commands and now it works! Many thanks!
(I also used the same folder, you used in your post but I don't know if this has any influence, just made it easier for me to check the fields and make the new input.)
-
@Capsia
Big Thanks!!!I also had problems like @herr-b -
NetworkManager ... result="success" ... Started the VPN service ... ... Saw the service appear; activating connection ... ... <error> ... vpn-connection ... Failed to request VPN secrets #3: No agents were available for this request.But I followed nmcli steps and got it working with custom gateway port.
I'll soon update first post for solution and change title to solved.
Once again thank You

-
@herr-b said in [SOLVED] PiVPN with PiHole home server. UT client configuration [step-by-step]:
(I also used the same folder, you used in your post but I don't know if this has any influence, just made it easier for me to check the fields and make the new input.)
Any directory should be fine, I've just used the same as on my pc to make checking easier
